How to implement HTTP Strict Transport Security (HSTS)
HTTP Strict Transport Security (HSTS) is an easy to implement measure to improves the security of websites that are fully reachable through TLS (SSL).
HTTP Strict Transport Security (HSTS) is an opt-in security enhancement that is specified by a web application through the use of a special response header. Once a supported browser receives this header that browser will prevent any communications from being sent over HTTP to the specified domain and will instead send all communications over HTTPS. It also prevents HTTPS click through prompts on browsers.
(Source and more information on [owasp.org] (https://www.owasp.org/index.php/HTTP_Strict_Transport_Security_Cheat_Sheet))
The standard is described in detail in RFC6797.
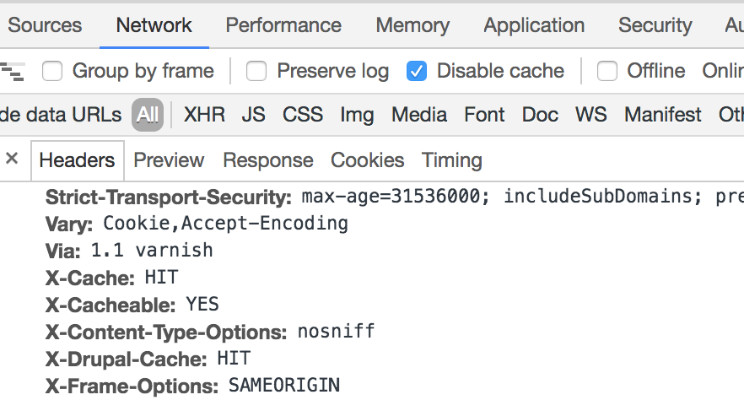
The header is very simple to implement: Strict-Transport-Security: max-age=<in seconds>
Optionally, subdomains can be included and some browsers can be instructed to preload the header. Domains can also be submitted manually to the preload list: https://hstspreload.org/ - but this requires a valid HSTS header first.
Once you request HSTS to be implemented, there are two elements to be checked first:
- Does the whole website use TLS exclusively (including any external content included)? If yes, then HSTS can be implemented at least without subdomains
- Does the affected domain have any subdomains (i.e. vpn.unic.com) that are not TLS-enabled? If no, the subdomains can be included or if all subdomains are TLS-enabled, then includeSubDomains can be set.
The following table shall provide help which header to implement:
| Header | max-age | Include Subdomains | Preload | Security | Likelihood of negative impact |
|---|---|---|---|---|---|
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload |
1 year | Yes | Yes | Very High | High |
Strict-Transport-Security: max-age=31536000; includeSubDomains |
1 year | Yes | No | High | High |
Strict-Transport-Security: max-age=31536000 |
1 year | No | No | High | Low |
Strict-Transport-Security: max-age=86400 |
1 day | No | No | Medium | Low |
A shorter max-age allows a faster reaction in case anything goes wrong.
How to choose which header to set
As such, we recommend the following approach (adapted from https://hstspreload.org).
- Ensure all content of the site works properly over HTTPS.
- Examine and fix any redirects - especially from HTTP to HTTPS and from domain to subdomain (i.e. unic.com to www.unic.com)
- Ensure the TLS certificate and the complete chain is valid for the domain and any subdomains redirects point to
- Add the Strict-Transport-Security header to all HTTPS responses and ramp up the max-age in stages, using the following header values: 5 minutes (300), 1 day (86400) and 1 week (604800).
- During each stage, fix any problems that come up and then wait for the full max-age of the stage before you move on (e.g. wait a week in the last stage).
- Once you’re confident that there will be no more issues, increase the max-age to 1 year (315360000)
- Examine all subdomains (and nested subdomains) of your site and make sure that they work properly over HTTPS.
- For best security, set:
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload - Submit the site to be preloaded via https://hstspreload.org.
Redirects and Subdomains
Ideally, the HSTS header is set on the top level domain independent of the protocol. It’s important for any redirect to first go to https and only then to any subdomain, i.e.: unic.com -> http://unic.com -> https://unic.com -> https://www.unic.com. Otherwise, it’s not possible to submit the domain to the preload include list.
How to set HSTS headers
Implementation details depend on the type of webserver used. Mozilla has an excellent [SSL Configuration Utility] (https://mozilla.github.io/server-side-tls/ssl-config-generator/).
Tools
You can use https:observatory.mozilla.org or https://www.ssllabs.com/ssltest/ to check for HSTS headers.
Enabling HSTS is a simple, yet effective way to increase the security of your users, data, and websites at no additional cost.